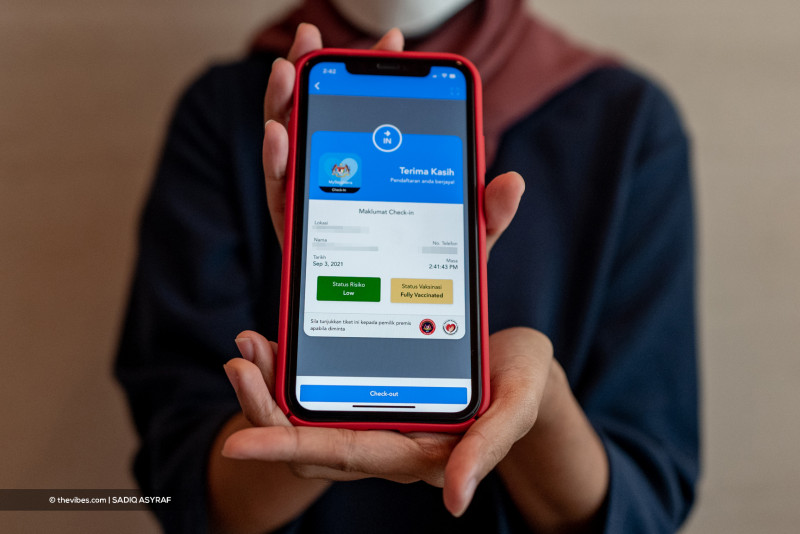
KUALA LUMPUR – An account with full access to security settings and administrative features of the Covid-19 tracking app MySejahtera downloaded data on three million vaccine recipients over the span of three days.
This was revealed in the Auditor-General’s Report 2021, which stated that the account, a “Super Admin” approved by the Health Ministry, began downloading the information on October 28, 2021 with the help of multiple internet protocol (IP) addresses.
“Audits on the user data for administrative matters found that the Super Admin account has MySejahtera vaccine administrator access.
“The vaccine admin allows (those with access) to upload or download vaccination appointments, exemptions, and records individually or in bulk from the MySejahtera database,” the report released today said.
It added that it “cannot confirm” the exact data downloaded from MySejahtera by the account.
Recommending that the data security management on the MySejahtera app be tightened to ensure the safety of vaccine recipient’s data, the report also said that the Health Ministry had cancelled the account on November 2 – two days after the final download.
While a police report on the incident was lodged on November 5, other safety measures were put in place, including informing the National Cyber Security Agency to block any repeated requests from the same source.
Citing a response from the ministry on September 9 and October 7 this year, the report said that the ministry is still attempting to determine the exact information acquired by the account.
“(During the first MySejahtera security meeting last year), the supplier stated that on October 28, 2021, a Super Admin account with registration approval from the Health Ministry was misused.
“As soon as the matter was identified by the suppliers, the account was blocked immediately,” the response detailed.
The ministry added that while the case is still being investigated by the Royal Malaysian Police, it will continue to work together with authorities to secure more information and identify the culprit behind the event.
Besides that, the report also highlighted that a single IP address had attempted 1.12 million times to break into the MySejahtera app database.
The attempts had begun on 27 October, 2021 – the day before the Super Admin attack – following which MySejahtera developers Entomo Malaysia had taken down the IP address and installed a firewall on November 1.
A note from the ministry included in the report stated that a separate police report on the matter was also lodged on November 5 while remedial measures were taken.
Concerns had previously been raised over the possibility of security and data breaches within MySejahtera after scores of users expressed alarm over receiving unsolicited emails and OTP messages from the app.
The Health Ministry had subsequently responded by saying that the false emails and text messages were the result of misuse of the MySejahtera app’s programming interface, and not due to a database leak. – The Vibes, February 16, 2023






















.jpg)

